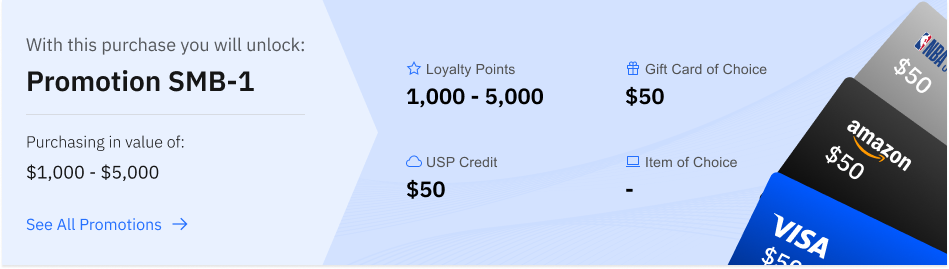
Our latest release continues the tradition of delivering integrated innovations. New features will help you extend security into branch offices, apply security dynamically to users, and provide better visibility for mobile users connecting to your network.
World-Class Security + High-Performance Connectivity
With industry-leading security natively integrated into our SD-WAN solution, you get all the security features from our Next-Generation Firewalls – powered by PAN-OS® 9.1 – together with Zero Touch Provisioning (ZTP) and the SD-WAN functionality from a single vendor.
Consume our secure Prisma™ Access SD-WAN hub as a service, or build the hub and interconnect infrastructure yourself using our Next-Generation Firewalls.
Regardless of the deployment model, this tight integration allows you to manage security and SD-WAN on a single intuitive interface.
Dynamic Security Actions with Automated Enforcements
User access policies based on static directory information are simply not enough in today’s dynamic environment.
Network and security teams are tasked with providing correct access to users. But creating ad hoc rules to provide time-bound access to workers – and then ensuring these rules are removed once the business need is over – is manual, time-consuming and poses a security risk if the rules become over-provisioned.
In addition, the inability to dynamically change a user's access based on information about their behavior results in tedious operations and increased security risks.
With PAN-OS 9.1, you can enable Dynamic User Groups (DUG) and reap these benefits:
Automatically include users as members without manually creating and committing policy or group changes.
Still maintain user-to-data correlation at the device level before the firewall even scans the traffic.
Configure and manage a single security policy to auto-remediate anomalous behavior and malicious activity while maintaining user visibility.
Enhanced Visibility and Troubleshooting for GlobalProtect Deployments
PAN-OS 9.1 provides greater visibility, rapid troubleshooting, and enhanced logging enhancements to help you monitor and rectify connection failures with your GlobalProtect™ deployments.
The logging enhancements are available for any Palo Alto Networks Next-Generation Firewall deployed as a GlobalProtect gateway or portal or in a Prisma Access mobile user deployment.
1. Throughput is measured with App-ID and logging enabled, with 64 KB HTTP/appmix transactions.
2. Disable Server Response Inspection (DSRI) throughput is measured with App-ID, IPS, antivirus, anti-spyware, WildFire, file blocking, and logging enabled, utilizing 64 KB HTTP transactions.
3. Threat Prevention throughput measured with App-ID, IPS, antivirus, anti-spyware, WildFire, and logging enabled, utilizing 64 KB HTTP/appmix transactions.
4. IPsec VPN throughput is measured with 64 KB HTTP transactions and logging enabled.
5. New sessions per second is measured with application override, utilizing 1 byte HTTP transactions.
6. Adding virtual systems to the base quantity requires a separately purchased license.